Warning: Undefined array key "eael_show_read_more_button" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Elements/Post_Block.php on line 845
Warning: Undefined array key "eael_post_block_layout" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Elements/Post_Block.php on line 865
Warning: Undefined array key "eael_post_tiled_column" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Elements/Post_Block.php on line 873
Warning: Undefined array key "enable_post_block_image_ratio" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Template/Post-Block/default.php on line 19
New Law to Boost Healthcare Cybersecurity: 5 Critical Changes You Need to Know in 2024
Warning: Undefined array key "eael_show_post_terms" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Template/Post-Block/default.php on line 243
The healthcare sector is grappling with unprecedented cybersecurity challenges, prompting a bipartisan group of U.S. senators to introduce the Health Care Cybersecurity and Resiliency Act...
Warning: Undefined array key "enable_post_block_image_ratio" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Template/Post-Block/default.php on line 19
Innovations in Cybersecurity: New Tools and Strategies Unveiled
Warning: Undefined array key "eael_show_post_terms" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Template/Post-Block/default.php on line 243
In a rapidly evolving digital landscape, cybersecurity remains a top priority for organizations worldwide. Recent innovations from major players like AWS, Tuskira, and Nozomi Networks...
Warning: Undefined array key "enable_post_block_image_ratio" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Template/Post-Block/default.php on line 19
Empowering Communities Through Cybersecurity Training Initiatives
Warning: Undefined array key "eael_show_post_terms" in /home/techsupp/public_html/wp-content/plugins/essential-addons-elementor/includes/Template/Post-Block/default.php on line 243
In an era where digital threats are increasingly prevalent, various organizations are stepping up to provide essential cybersecurity training to diverse groups. Notably, Azercell, a...

Emerging Cybersecurity Threats and Trends: What to Expect in 2025
As we approach 2025, the cybersecurity landscape is evolving rapidly, with new threats emerging from unexpected sources. Recent forecasts highlight a significant rise in cyber threats, particularly from teenagers and employees trained in artificial intelligence (AI). Organizations must prepare for these challenges to safeguard their data and operations. Key Takeaways AI-Driven Threats: The integration of AI in business operations will create new vulnerabilities. Youth Involvement in Cybercrime: An increase in cybercrime among teenagers is anticipated. Internal Fraud Risks: Employees with AI training may exploit their knowledge for illicit activities. Power Infrastructure Vulnerabilities: Data centers are becoming prime targets for cybercriminals. Dynamic Identification Systems: The need for advanced identification methods is critical to combat fraud. AI Will Enhance Business Operations Organizations are expected to adopt AI-powered

Cybersecurity Market Trends and Predictions: A Look Ahead to 2025
The cybersecurity market is poised for significant growth, driven by increasing digital threats and the rising importance of data privacy. As organizations invest in advanced security solutions, the market is projected to expand from $193.73 billion in 2024 to $562.72 billion by 2032, reflecting a compound annual growth rate (CAGR) of 14.3%. This article explores key trends and predictions shaping the cybersecurity landscape in the coming years. Key Takeaways The global cybersecurity market is expected to grow significantly, reaching $562.72 billion by 2032. Key drivers include the rise of e-commerce, increased government spending, and the integration of AI and machine learning in security solutions. Regulatory frameworks are evolving to address cybersecurity challenges, particularly in critical sectors. Market Growth Drivers The cybersecurity market is influenced by

Cybersecurity Incidents and Responses: A Growing Concern
In recent weeks, the cybersecurity landscape has been shaken by significant incidents, prompting organizations worldwide to reassess their security measures. Notably, the Indian online ID verification service Signzy confirmed a cyberattack that raised alarms about the security of its clients, including major financial institutions. Meanwhile, Germany is ramping up its cybersecurity efforts in response to increasing threats from foreign adversaries. Key Takeaways Signzy confirmed a cyberattack affecting its operations and clients. Germany is enhancing its cybersecurity measures amid rising threats from Russia and China. A recent study revealed that one in five companies cannot recover data after a cyberattack. Signzy’s Cybersecurity Incident Signzy, a prominent provider of online ID verification services, acknowledged a cybersecurity incident that occurred last week. The company, which serves over 600

Understanding Cybersecurity: Essential Strategies for Protecting Your Digital Life
In our increasingly digital world, understanding cybersecurity is crucial for safeguarding our personal information and online activities. As cyber threats grow in number and sophistication, individuals must equip themselves with essential strategies to protect their digital lives. This article outlines key concepts and practices in cybersecurity, empowering readers to navigate the online landscape safely and confidently.

Essential Cybersecurity Solutions for SMBs: Protecting Your Business in the Digital Age
In today’s digital world, small and medium-sized businesses (SMBs) face a growing number of cybersecurity threats. It’s crucial for these businesses to understand the risks and implement effective solutions to safeguard their data and operations. This article explores essential cybersecurity solutions for SMBs, helping them navigate the complexities of protecting their business in an ever-changing landscape. Key Takeaways Cybersecurity risks are constantly changing, making it essential for SMBs to adopt a multi-layered defense strategy. Employee training is vital; staff should know how to recognize threats like phishing and use strong passwords. Regularly updating software is crucial to close security gaps and protect against new vulnerabilities. Investing in comprehensive cybersecurity tools can help protect against various threats, including malware and ransomware. Backup solutions are necessary to

Unlocking Growth: Managed IT Services in Austin for SMBs
In today’s fast-paced world, small and medium businesses (SMBs) in Austin face many challenges. One of the best ways to overcome these hurdles is through managed IT services. These services not only help businesses run smoothly but also support their growth. This article explores why managed IT services are essential for SMBs in Austin and how they can unlock new opportunities for success. Key Takeaways Managed IT services help SMBs in Austin save money and time. These services can protect businesses from cyber threats and data breaches. Choosing the right IT provider is crucial for effective support. Flexible IT solutions can grow with your business needs. Real success stories show how local businesses have thrived with managed IT services. Understanding the Importance of Managed IT

Top 3 Endpoint Detection and Response (EDR) Solutions and How Tech Support Austin Can Implement Them
In today’s cybersecurity landscape, Endpoint Detection and Response (EDR) solutions are crucial for protecting businesses from sophisticated threats. As your local managed service provider, Tech Support Austin is equipped to implement and manage these advanced security tools for your organization. Let’s explore the top three EDR solutions and how we can help you leverage them effectively.
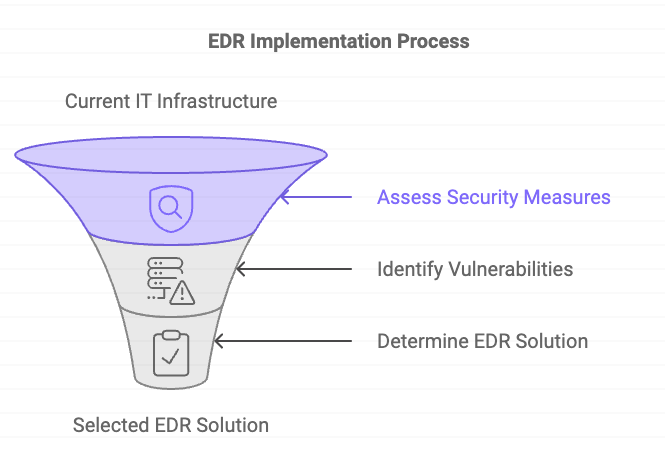
Understanding Endpoint Detection and Response (EDR) and Its Importance for Your Business
In today’s rapidly evolving digital landscape, cybersecurity threats are becoming increasingly sophisticated and prevalent. As a result, businesses of all sizes need robust security measures to protect their valuable data and systems. One crucial component of a comprehensive cybersecurity strategy is Endpoint Detection and Response (EDR).




